THE investment bank, despite billions in annual revenue and the small squadron of former police, military and security officers on its payroll, was no match for Mark Seiden.

Interview: Mark Seiden
In a downloadble MP3 containing interview excerpts, computer security expert Mr. Seiden talks about how he breaks into systems, identity theft and how to protect yourself in the information age. (22:05)
Toiling Through the Drab, Oily Dregs (May 5, 1997)
"Tell me the things you most want to keep secret," Mr. Seiden challenged a top executive at the bank a few years back. The executive listed two. One involved the true identities of clients negotiating deals so hush-hush that even people inside the bank referred to them by using a code name. The other was the financial details of those mergers and acquisitions.
A week later, Mr. Seiden again sat in this man's office in Manhattan, in possession of both supposedly guarded secrets. As a bonus, he also had in hand a pilfered batch of keys that would give him entry into this company's offices scattered around the globe, photocopies of the floor plans for each office and a suitcase stuffed with backup tapes that would have allowed him to replicate all the files on the bank's computer system.
"Basically, that all came from working nights over a single weekend," he said with a canary-eating smile that seemed equal parts mischief and pride.
Mr. Seiden is what some people inside the security industry call a "sniffer": someone who is paid to twist doorknobs for a living, to see which are safely locked and which are left dangerously unsecured. Clients sometimes hire Mr. Seiden, a former computer programmer, to buttress the security systems that protect their computers and other precious corporate assets. But primarily, large corporations turn to him to test the vulnerability of their networks.
"Mark is one of the more respected people out there doing this kind of work," said Bruce Schneier, a security expert and the author of "Beyond Fear: Thinking Sensibly About Security in an Uncertain World." Mr. Schneier called him "one of the good guys."
And for Mr. Seiden and others practicing the strange craft of intrusion detection, business has never been better. As data-security breaches at places like ChoicePoint and LexisNexis have made headlines, there has been a "tremendous surge in vulnerability assessments" in recent months, said Howard A. Schmidt, a former chief security officer at Microsoft who has also worked inside the White House on cybersecurity issues.
Indeed, purloined Social Security and credit card numbers are the new top prizes of the 21st-century cybercriminal. "In the early days of the Internet, breaking into systems was about bragging rights. It was about technical prowess. It was breaking into systems just to break in," said Mr. Schmidt, who is now working as an independent security consultant in Issaquah, Wash. "Now what we're seeing are economic crimes in a way we've never seen before."
That is why corporations and other large organizations are increasingly turning to people like Mr. Seiden to assess the soundness of their security systems. No one knows how many people make their living doing what people in the industry call penetration testing, though clearly their numbers are climbing. The most recent Computer Crime and Security Survey - released earlier this month by the F.B.I. and Computer Security Institute, an information security trade group - said that more than 87 percent of the organizations they polled conduct regular security audits, up from 82 percent a year earlier.
"Since the beginning of the calendar year we've seen a great increase in the number of calls from enterprises looking for someone to do security vulnerability testing for them," said Kelly M. Kavanagh, an analyst who tracks the security industry for Gartner Inc., a technology research group.
CORPORATIONS in North America spent more than $2 billion on outside security consultants in 2004, Mr. Kavanagh said. That was up 14 percent from the previous year.
As a result of all that spending, a large organization's data center - whether it holds a company's most precious trade secrets or the credit card numbers of millions of customers - is generally much better protected than it was just a few years ago. Yet that has meant only that the bad guys, and those in the business of thwarting them, must become more creative.
"Most systems are like this Tootsie Roll Pop," Mr. Seiden said. "They have this hard, crunchy outside, but they're very gooey and soft inside. And once you get past that crunchy outside and you're inside, you can do anything." Nowadays, cybercriminals are more likely to gain access to a computer system by picking a lock or cleverly bluffing their way inside a building than by outsmarting those who run a company's data center.
To keep pace, sniffers must do their best to think like an enterprising thief. Mr. Seiden, who divides his time between residences in Manhattan and Silicon Valley, has a closetful of uniforms he has gathered rummaging through thrift shops and browsing on eBay. The collection includes the distinctive purple and green polo shirts worn by FedEx drivers, shirts from various architectural design firms and the windbreaker worn by the Iron Mountain employees who drive their homely Ford Econoline 350's around America's streets picking up backup files - and, occasionally, losing those files. (In May, Time Warner, one of Iron Mountain's clients, disclosed that the Social Security numbers of 600,000 of its current and former employees went missing while in Iron Mountain's care.)
Mr. Seiden is also apparently quite handy with the tools that criminals use to pick locks, and he is something of a legend inside security circles for figuring out that the easiest way for an intruder to get inside a locked room is sometimes through the ceiling, in the space between the actual ceiling and the tiles dropped down a couple of feet to make room for ventilation equipment.
"Mark is known for his more creative solutions to security problems," Mr. Schneier said.
Mr. Seiden's girlfriend complains that the two of them will visit a museum but that he will barely take time to notice the art because he's too busy assessing the security system. He will visit a new apartment and provide, unbidden, a critique of the building's buzzer system, the relative worthiness of the front door and the cheap hunk of brass that most people would consider a worthy lock. Walking down the street, Mr. Seiden seems almost offended when passing a storefront that has an oversized safe, seemingly impenetrable, sitting in plain sight.
"All I'd have to do is put up a tiny camera here," he says, shaking his head, "and I'd have a recording of the combination when someone unlocks it."
In Mr. Seiden's presence, it's easy to find yourself feeling suddenly paranoid. Passing an automated teller machine prompts him to recount the time an employee of an A.T.M. manufacturer was arrested, suspected of putting a piece of hacked code inside around 100 machines - a surreptitious way for a band of thieves to capture people's secret passwords and the data embedded on their swipe cards. And don't even get him started about airports and the security flaws he spots every time he travels.
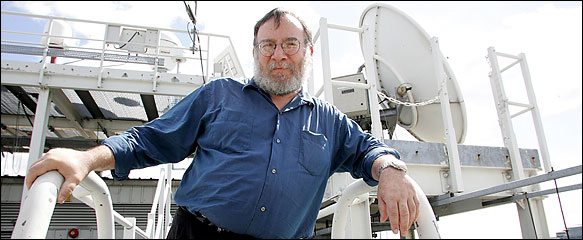
Standing 5-foot-7, Mr. Seiden is shaped vaguely like the Buddha. He is 54 years old and friendly in a way that makes it easier for him to talk his way into places. He seems to have a gift for blending in; he says he finds that if he carries a clipboard and looks officious, no one bothers to question his presence. But he is a man with a robust ego who enjoys the limelight. He wears glasses and a thick beard littered with gray and, when not in costume, he tends to dress in classic high geek: sandals and shorts, even when there's a decided chill in the air, and T-shirts that are either tie-died or freebies that promote an obscure technology product.
Mr. Seiden seems the computer-world equivalent of the police officer motivated to join the force at least in part by his desire to drive too fast and to carry a gun. His eyes twinkle playfully when sharing his tricks of the trade, like his propensity for lingering around a taco truck while construction workers are on break and then casually walking among them, hard hat under arm, suddenly inside a supposedly secure site.
In a sense, Mr. Seiden's career as an accomplished intruder working on the side of good began while he attended Columbia University in the late 1960's. He studied mathematics and linguistics but, as he described it, spent most of his time working at the radio station. He was at Columbia when students commandeered buildings and the police sprayed the protesters with tear gas. To gain access to the story as it was unfolding, he learned the tunnel system that honeycombed the campus and figured out how to pick locks so that he could enter from below the buildings that students were occupying.
He taught himself computer programming while attending the Bronx High School of Science. His earliest jobs were as a computer scientist inside some of the country's more prestigious research facilities and technology companies, including I.B.M. and Bell Laboratories. His résumé from those years also includes stints as a recording engineer and one doing the sound and lighting for a dance troupe. In 1983, feeling burned out after two years at a Silicon Valley start-up, he ventured out on his own, hanging out his shingle as a computer consultant. Seven years later, a friend asked his help in designing a system that allowed people to use a credit card safely over the Internet - and Mr. Seiden was hooked. From that day, network security became his specialty.
"If you're serious about creating a secure system, you need two people to do it," he said. "You need someone who sets it up and one who checks it. Different people see different things; people have different strengths. And people make mistakes."
Mr. Seiden may qualify as something of a supergeek, but over time he has found that it's often the nontechnical and mundane that he is best able to exploit. A perfect example is that investment bank whose most precious secrets he was able to learn in only a few days. (Mr. Seiden would talk about the bank, a widely recognized brand, only if its name was not used.)
The bank may have had in place some of the best security software that money could buy, but just by having a badge that the bank routinely grants outside consultants, he was able to roam the building as he wanted. That badge didn't grant him access to the computer room, but it didn't matter. He figured out the location of the facilities department and discovered that the schematics for the bank's headquarters, and the master keys, were stored inside a filing cabinet that it took a minute or two for him to pick.
While strolling around, he also found the backup tapes to the bank's central computers sitting in suitcases, "so I walked away with a set of backups," he said.
WITH a master key, he knew that he could get into any office in the bank's main headquarters. Then he used what he fancifully called "social engineering techniques" - meaning that he picked up a phone and, pretending to be a banker inside the company, called the accounting department, and asked: Whom should someone contact to assign a code name to a project?
"The clerk who assigned code words left that stuff in folder in a file cabinet," he said. "It was in a locked area in a locked office - so why would she have to lock the file cabinet?" Of course, even if she had locked the file cabinet, Mr. Seiden would have been able to pick the lock.
In the end, however, there is only so much that can - or should - be done to keep the villainous at bay. "Given a decent budget, I can break into any network," said Mr. Schneier, the author. "The real question is to what extent is it critical to defend." Vulnerability testing is something that any company must do, he said, but security is always a matter of trade-offs. As security experts like Mr. Schneier often say, one could build a more secure house if it had no windows, but no one would want to live there.
"You need to recognize that you're not going to make a system 100 percent safe," said Richard Mogull, a Gartner analyst specializing in security. "But the truth is that 99.9 percent of the people you're protecting against have only rudimentary skills. And as much fun as it is to tell stories how you can get into almost any place, the reality is that you can waste a lot of time finding that one chink in the armor."
Mr. Seiden doesn't disagree that the benefits of vulnerability testing are limited. He tells of the six weeks he spent in Asia this year on behalf of a giant Internet company, one of his best clients. There he tested the security of the sites the company uses to house the computers that serve up its Web pages.
After Mr. Seiden proved that he could break into those facilities, his client installed video cameras so it could monitor the sites remotely.
"Basically you can't prevent a determined adversary who has unlimited resources from breaching security," he said. "What you want to do is prevent yourself from being taken and not know about it. At least if you know about it, you know what's been compromised and you can fix it up afterward."